Not all Autobots are good. When some of them roll out, they have one objective. To break into your WordPress site.

Leaving the Transformers reference behind, what kind of bot attacks do WordPress site admins need to be on guard against? Automated scripts that attempt to gain access to your site by trying to guess your login info. It could be a single bot or script, or a botnet, which is a whole group of bots working together.
Either way, they are surfing the net, checking the backdoors of hundreds of thousands of websites. They’re bad bots looking for a WordPress core version, plugin, or theme that has a known vulnerability.
How Automated Bad Bots Gain Access
It’s not hard for a hacker to find what they’re looking for. All WordPress vulnerabilities are documented, so as soon as they’re made public, all a hacker needs to do is create a script or application and release it into the world wide web. Call them bots, spiders, or crawlers, they’re looking for a weak spot to break in.
Unfortunately, many site owners think hackers target individual sites specifically and rationalize that their little WordPress site is so insignificant they’ll never be found.
That’s not the way it works. They’re right that there’s little chance they’re a specific target. Instead, imagine a fishing net casting out and hauling in thousands of little fish. That little website is just one little fish.
How do Bots Work?
Internet traffic is made up of a large percentage of bots. It’s their job to interact with webpages and or users and perform a variety of tasks. For example, chatbots, the social bots found on social media platforms, and even monitoring bots that keep an eye on the health of your website, network, or operating system.
Bots are essentially created from algorithm sets that assist them in performing the tasks they have been designed to do.
But what about the bad bots?
How Dangerous are Bad Bots?
All bad bots, spiders, and crawlers aren’t created equal.
Scraper Bots
First, there are—I suppose—legitimate reasons for scraper bots. However, cybercriminals use web scraping to collect data from websites for malicious purposes. This can include reselling your content or, if you’re an e-commerce site, extracting your prices for the purpose of undercutting you.
But that’s not all they can do. These crawlers find paths to navigate, read parameter values, and collect information on application or website operations. And it’s an expensive problem. Statista, a leading provider of consumer and market data, reports that e-commerce businesses lose about 2% of their revenue due to scraping.
In 2021, e-commerce sales in the US alone were $870 billion. 2% of that is $17.4 billion. Collectively, scrapers are making a lot of money, so they’re not going to stop anytime soon.
Email Bots
This type of bot looks for insecure forms, specifically contact forms. This can result in you receiving email spam or your WordPress site being used to send email spam, including links to malware, phishing, marketing messages, and so forth.
All of this is bad on a variety of levels, perhaps the worst being that your web host can ban your account because they assume you’re the one sending spam emails.
Comment Spam
If you have a WordPress site and you have comments enabled, there’s a good chance you’ve received comment spam. Again, this isn’t individual people leaving spam, these are spambots that exist to post unsolicited comments and advertisements on your site, typically with links included.
In some cases, links are left to generate backlinks in the hopes of providing some SEO benefits — which does not work!
Login Spamming
Login spamming is similar to a brute force attack, where hackers try to crack passwords, encryption keys, and login credentials by working through a list of all possible combinations until they hopefully find the right one. Since this is digitally driven, they can run through thousands of combinations every minute.
Varonis, an enterprise data protection company, describes a brute force attack as the “cyberattack equivalent of trying every key on your key ring, and eventually finding the right one.”
How to Protect Yourself from Automated Bot Attacks
With all these bad bots, spiders, and crawlers loose on the Internet, what can you do to keep your WordPress site protected?
Fortunately, there are several options.
Depending on the type you use, bot protection can help you guard against brute force attacks, web scraping, and more.
Use a Comprehensive Security Plugin
There are many security plugins to choose from. Whatever you choose, you want something that can identify and stop malicious behavior before it finds its way to your website. And in the event your site does get hacked, a plugin can help you investigate and repair it.
A few top-rated security plugins include:
- All-in-One Security
- iThemes
- Sucuri
- Wordfence
Block Content Form (Email) Spam
If you’re getting a lot of spam messages through the contact form on your website, there are a few ways to fix this.
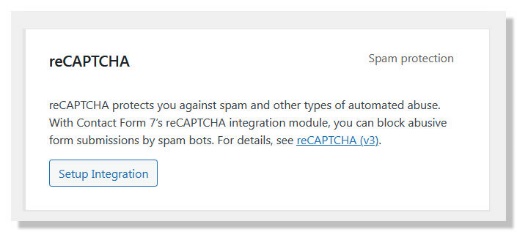
ReCAPTCHA. This is a free tool made available by Google. Most of the popular contact form plugins such as Contact Form 7 and WPForms have this integrated, you simply need to enable the feature.
Here’s an example from the Contact Form 7 integration panel.
Block Comment Spam
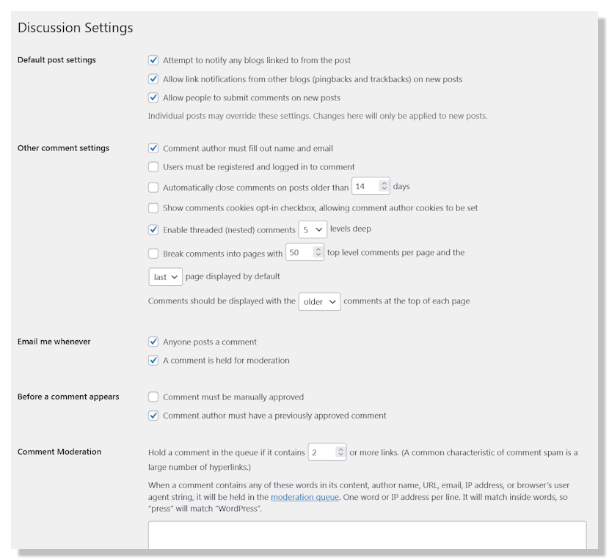
WordPress comes with some built-in features that will help you block comment spam.
From your WordPress dashboard head to Settings >Discussion. On this page, you can change your default comment settings, including disabling comments sitewide.
Some other options are to disable the following:
- Anonymous comments
- Comments in individual posts
You also have the option to allow or enable:
- Comment moderation
- Comments from registered, logged-in users only
You can even blacklist a custom list of words or ban links in the comments.
Monitor for Bot Activity on Your WP Site
Unfortunately, none of these methods is foolproof. With that in mind, having a plugin that will monitor and log all relevant activity on your site is a good practice.
If you have a security plugin that notifies you when bot attacks happen, check out our plugin WP Admin Audit. With it, you can go a step further, examining logins to determine if they’re a security threat.
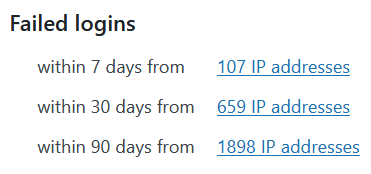
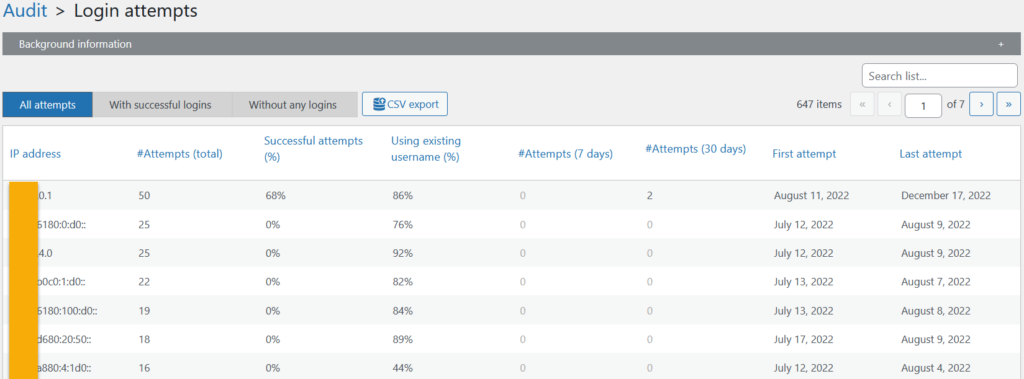
The login attempts can be analyzed in detail.
This answers questions like:
- Which IP addresses are the main source?
- How often did login attempts occur?
- Were any login attempts successful?
Want to try it out?
Download the free version at WordPress.org or checkout pricing.